Ever gotten a notice in the mail that read, something to the effect of, “by law, we’re required to inform you that since our infrastructure passwords were extremely weak, such as “password” and “123456,” a data breach has occurred and your personal information may or may not be in the hands of Russian hackers for sale somewhere in the deep web?”
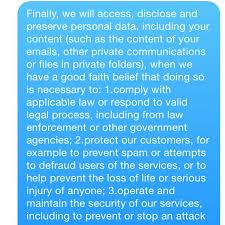
Well, maybe not that forthcoming, but you know what I’m talking about. When it comes to data network security breaches, there are laws which specifically require an organization to disclose to its customers whenever there has been such a data breach. These laws go far beyond the ubiquitous Health Insurance Portability and Accountability Act, better known as HIPPA.
For instance, here in Arizona, under Revised Statute § 44-7501, (Conditionally Rpld.) it requires a person that conducts business in this state who becomes aware of a data breach shall conduct a reasonable investigation and after determining a breach in the security system shall notify all individuals affected.[1] Simply put, organizations are required, by law, to disclose the breach, make remedies to resolve it, and can be held responsible for any damages thereof.
Oftentimes, these data network security breaches and subsequent notifications will be accompanied with a free offer for credit monitoring. As a consumer, you should absolutely take it, if you aren’t’ already monitoring your credit through some other third party.
First and foremost, if you discover a data network security breach within your firm, promptly notify your clients and provide measures to protect their interests. More importantly, as an organization, there are several steps you can take to avoid such data network security breaches. Some are as simple as requiring strong password policy. Others include keeping your data stored in a secured, locked environment with very restricted access.
Password Policies
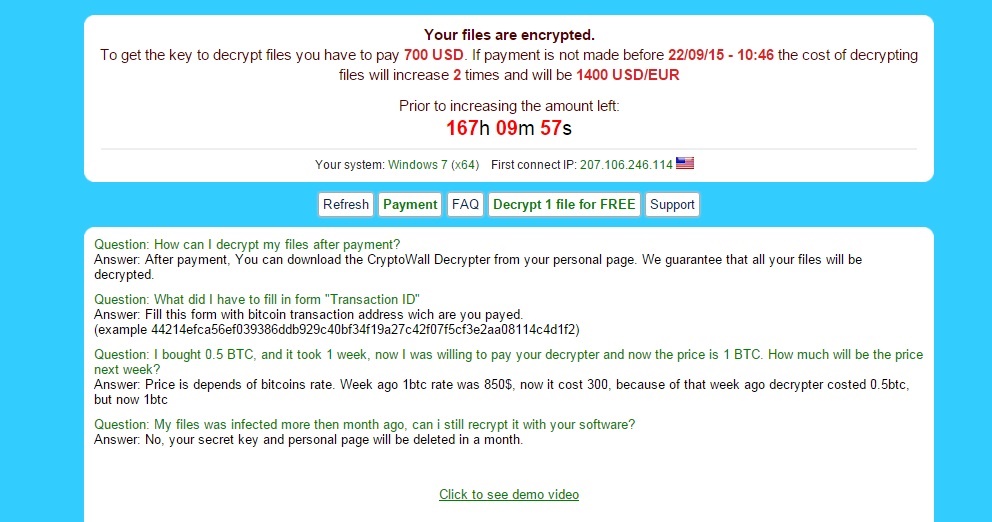
As both an end-user and as an administrator, I know how frustrating complex password policies can be. Yes it’s pain to have a password that must contain 1 uppercase letter, 1 lowercase letter, 1 symbol, 1 number, that cannot be anything you’ve ever used before and cannot have successive numerical values. However, that complexity exists for a reason. Hackers are well aware of the most commonly used password, such as “123456” followed by “password.”[2]
The folks at Microsoft recommend you “set password policy to require complex passwords, which contain a combination of uppercase and lowercase letters, numbers, and symbols, and are typically a minimum of seven characters long or more for all accounts, including administrative accounts, such as local administrator, domain administrator, and enterprise administrator.”[3]
However, consequently, when employees are required to change passwords often, meet minimum complexity requirements, and not repeat a password for a minimum amount of time, they may begin to break the rules and start writing passwords down simply because they cannot remember passwords that change so often.[4] Bottom line, design a password policy that is secure but doesn’t comprise functionality.

End-User Training
Many folks within an organization, while balking at having to change passwords regularly, simply do not understand the reasons behind it or the risks they attempt to advert. To that end, it would be wise for your IT staff to train end-users on why and how to keep their passwords unique and safe. Once employees discover their organization can be levied a hefty fine which may result in cutbacks as a consequence thereof, I’m sure the loudest of the balkers will begin to change their tune.
End-user training can be as simple as memo sent to employees requiring them to read, sign, and return to management. Alternatively, a once a year run-down presented by IT staff during a mandatory meeting should suffice for larger organizations.
Restricting Access
Your organizations most sensitive client data should be restricted to a need-to-know basis. If there is no need for the receptionist to access client information, then by all means create a security clearance group policy that only allows access to sensitive drives to those who truly require it.
Is your server room open to anyone at the firm? If so, quite frankly, you’re doing it wrong! I don’t care if there are 2 people in your firm, if one doesn’t need access to drives containing sensitive data, then by all means keep that access restricted. Unfortunately, many organizations have the “it’ll never happen to us” mentality that ultimately comes back to bite them in the end. Remember Target? Ever heard of the Panama papers?

Conclusion
Data security is your responsibility. Be not only aware of the legal obligations for your firm’s clients, but for anyone who does business with your organization. Develop corresponding IT policies and procedures to avoid liability that can possibly be the death knell of your organization.
[1] Arizona Revised Statutes, , http://www.azleg.state.az.us/FormatDocument.asp?inDoc=/ars/44/07501.htm&Title=44&DocType=ARS (last visited May 16, 2016).
[2] The 25 Most Popular Passwords of 2015: We’re All Such Idiots, , http://gizmodo.com/the-25-most-popular-passwords-of-2015-were-all-such-id-1753591514 (last visited May 16, 2016).
[3] Creating a Strong Password Policy: Logon and Authentication, , https://technet.microsoft.com/en-us/library/cc736605%28v=ws.10%29.aspx?f=255&MSPPError=-2147217396 (last visited May 16, 2016).
[4] Password Policy, , http://www.comptechdoc.org/independent/security/policies/password-policy.html (last visited May 16, 2016).